HBSRESOURCES
Papers
Deep dives into tech: unlock the next level of your technology knowledge.
Navigating Vendor Management
To ensure security up and down your supply chain, you’ll need to establish which partners you can trust with data. Creating a full vendor management program requires a significant investment, but this guide summarizes key first steps.
Download Guide
Download Guide
Incident Response Flow Chart
Developing an incident response plan and equipping your staff with the steps to execute that plan will give your organization its best chance at mitigating the negative impacts of a cyber-attack. Use this flow chart as a guide for how to respond to varying threat levels.
Download Guide
Download Guide
Business Impact Analysis Planner
A business impact analysis (BIA) provides a critical resource for making informed risk management decisions as it relates to the prioritization of your organization’s information systems to support the overall mission and business process. This planner will guide you through the first steps in conducting an effective BIA that points you towards the right investments for your overall risk assessment strategy.
Download Guide
Download Guide
Field Guide to Ransomware
Non-stop ransomware headlines prove that these attacks are everybody’s problem. This e-book will explain what organizations of every size need to know about preventing an attack—and limiting the damage if it happens to you.
Download Guide
Download Guide
10 Most Common Information Security Risks
We've compiled the risks our consulting team sees most frequently. This is where to focus to make the biggest difference in your security posture in the shortest period of time. Put these high-ROI jobs at the front of your IT team’s to-do list.
Download Guide
Download Guide

Employee Security Training Planner
This planner will help your organization to develop an effective security awareness and training program.
Download Guide
Download Guide
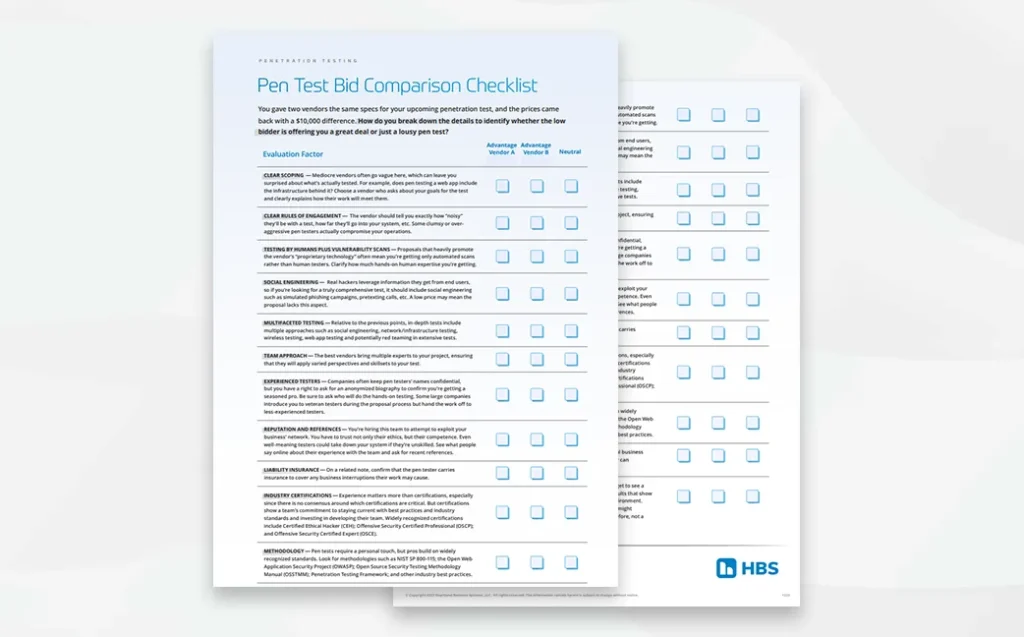
Pen Test Bid Comparison Checklist
You gave two vendors the same specs for your upcoming penetration test, and now you’re staring at two proposals with a $10,000 price difference. How do you break down the differences and identify whether the low bidder is offering you a great deal or just a lousy pen test? Use this guide to sort through the key factors for choosing a pen test that fits your goals.
Download Guide
Download Guide
Best Practices for Information Security Risk Assessments
This paper provides everything you need to know about this essential review from planning to execution to follow-up.
Download Guide
Download Guide
Trends in Electronic Evidence
In this paper, a U.S. Chief Magistrate Judge explains what she's looking for from attorneys and offers tips on how both sides in a case can winnow their work down to the ESI that really matters.
Download Guide
Download Guide
An IT Director’s Guide to Communicating Security Needs to the Executive Team
This paper discusses effective ways to communicate security concerns and solutions to the executive team – providing talking points and suggestions.
Download Guide
Download Guide
Digital Forensics Use Cases
Use this guide to understand how a digital forensics investigator can support your work in a variety of legal scenarios.
Download Guide
Download Guide
Four Essentials for Every Cybersecurity Plan
Follow these recommendations for password policies, network management, data security, and social engineering to help lay the groundwork for policies that protect your systems, your data and your organization's future.
Download Guide
Download Guide






